Defence & Public Safety Edge Computing Solutions
In defense and public safety, real-time situational awareness, resilience, and security are mission-critical. Systems deployed in the field — from drones and surveillance units to tactical vehicles and command centers — must operate reliably in air-gapped, low-connectivity, or high-risk environments, where traditional cloud solutions simply cannot reach.
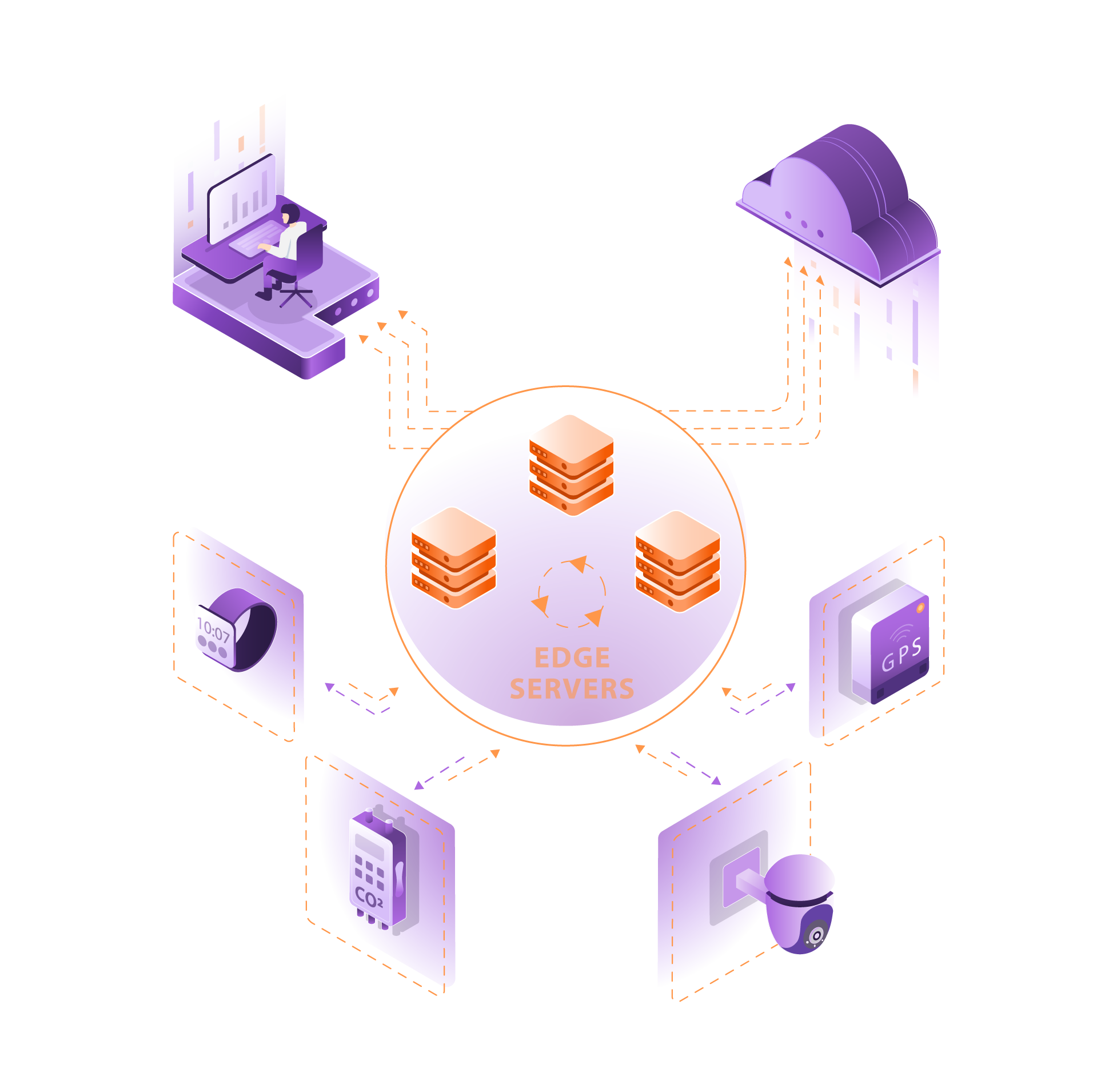
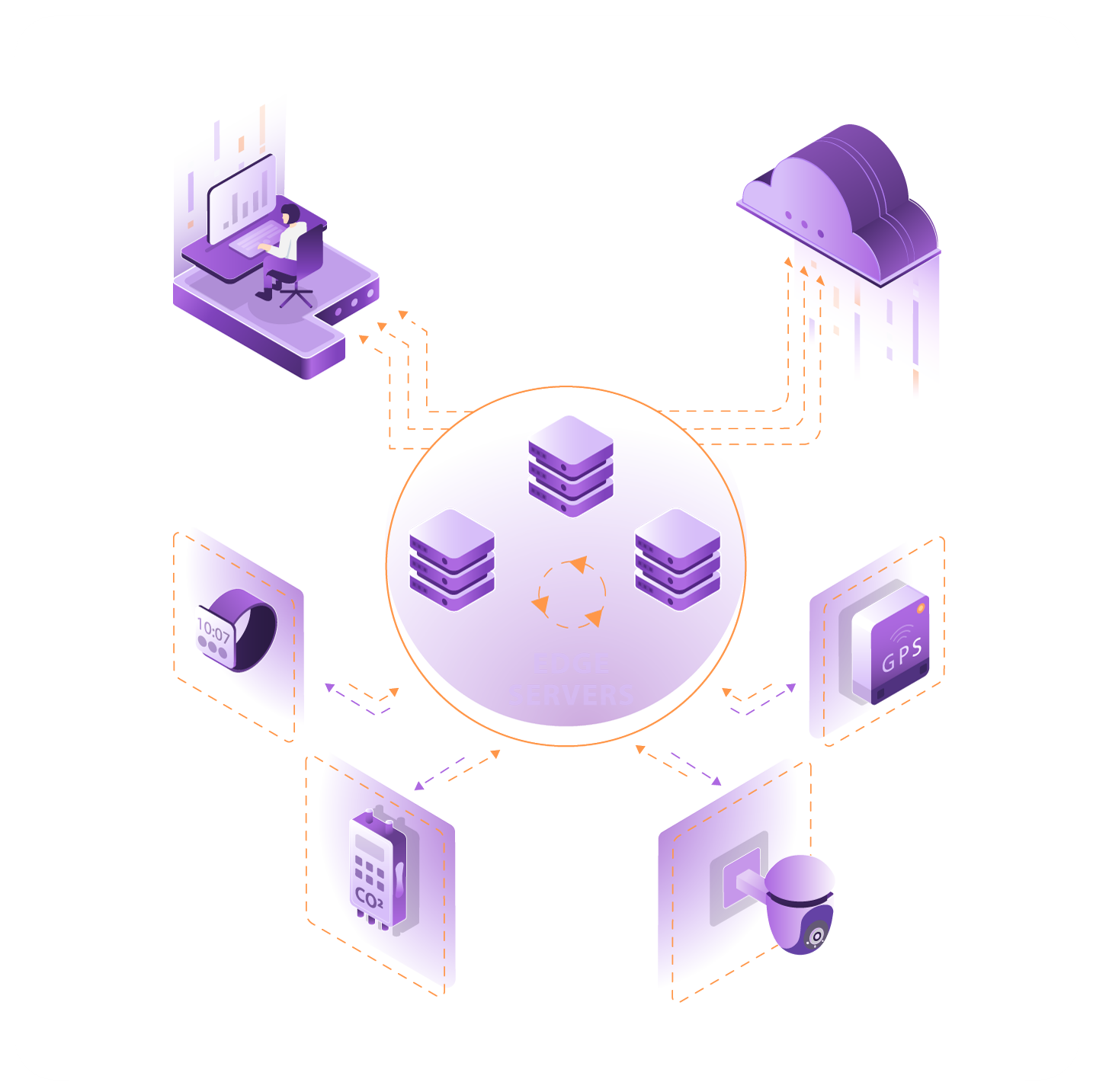
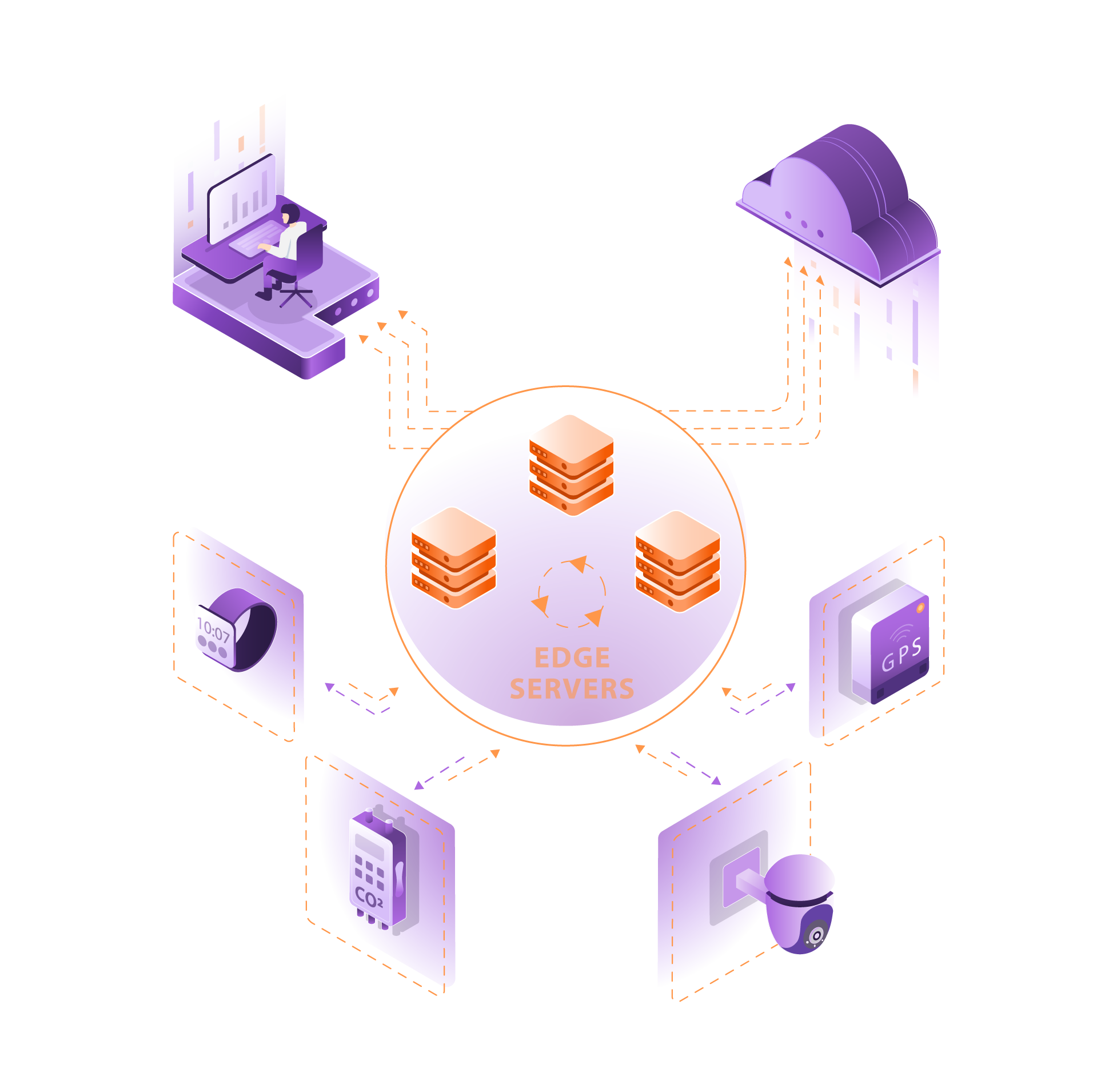
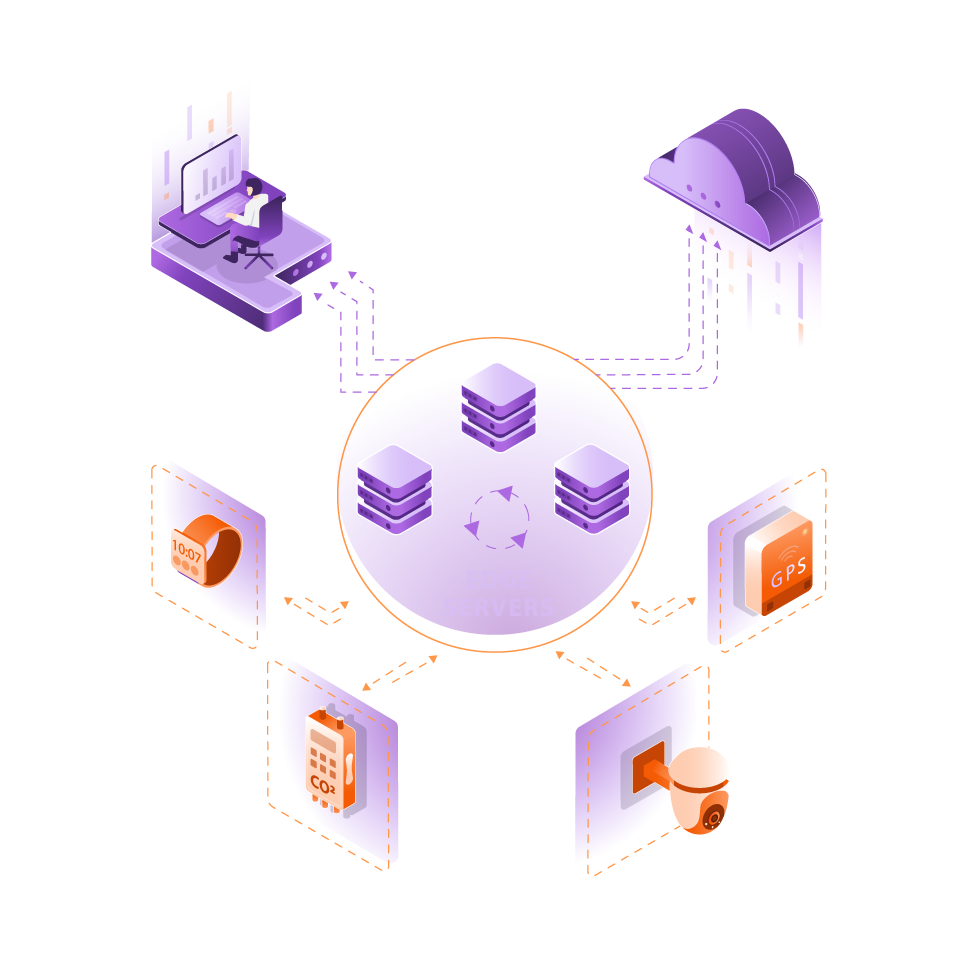
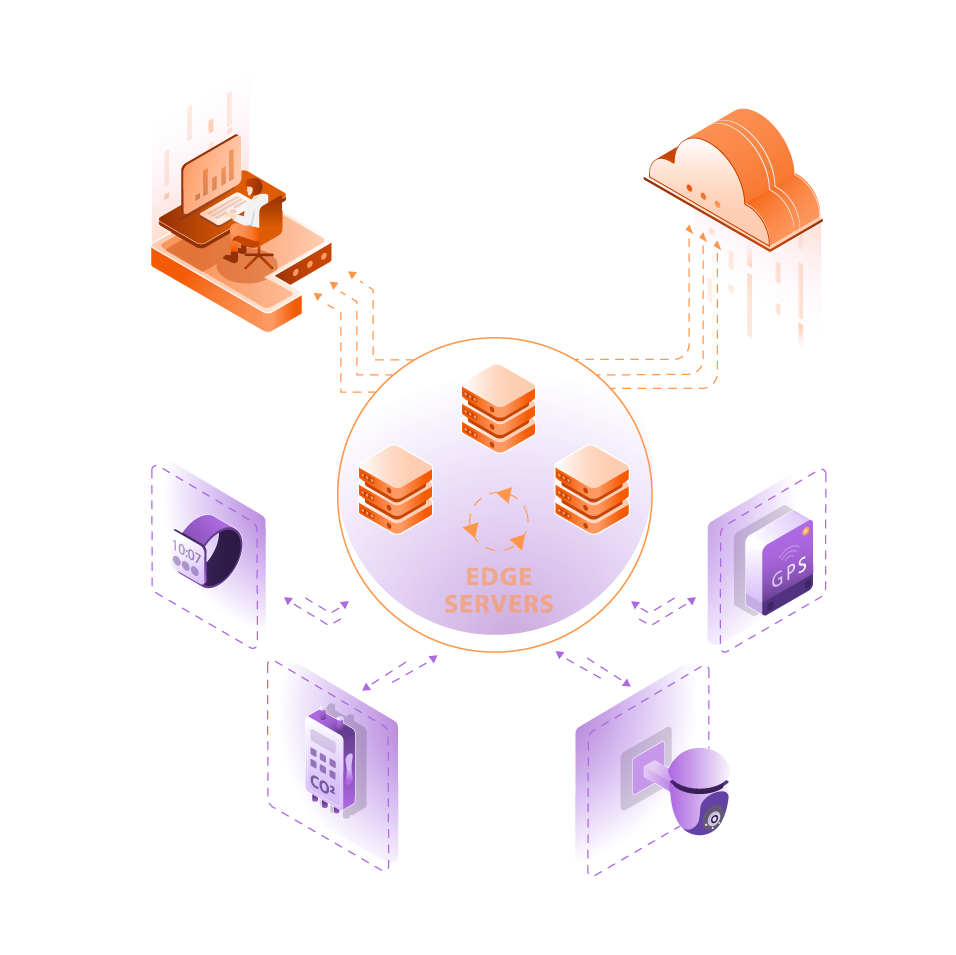
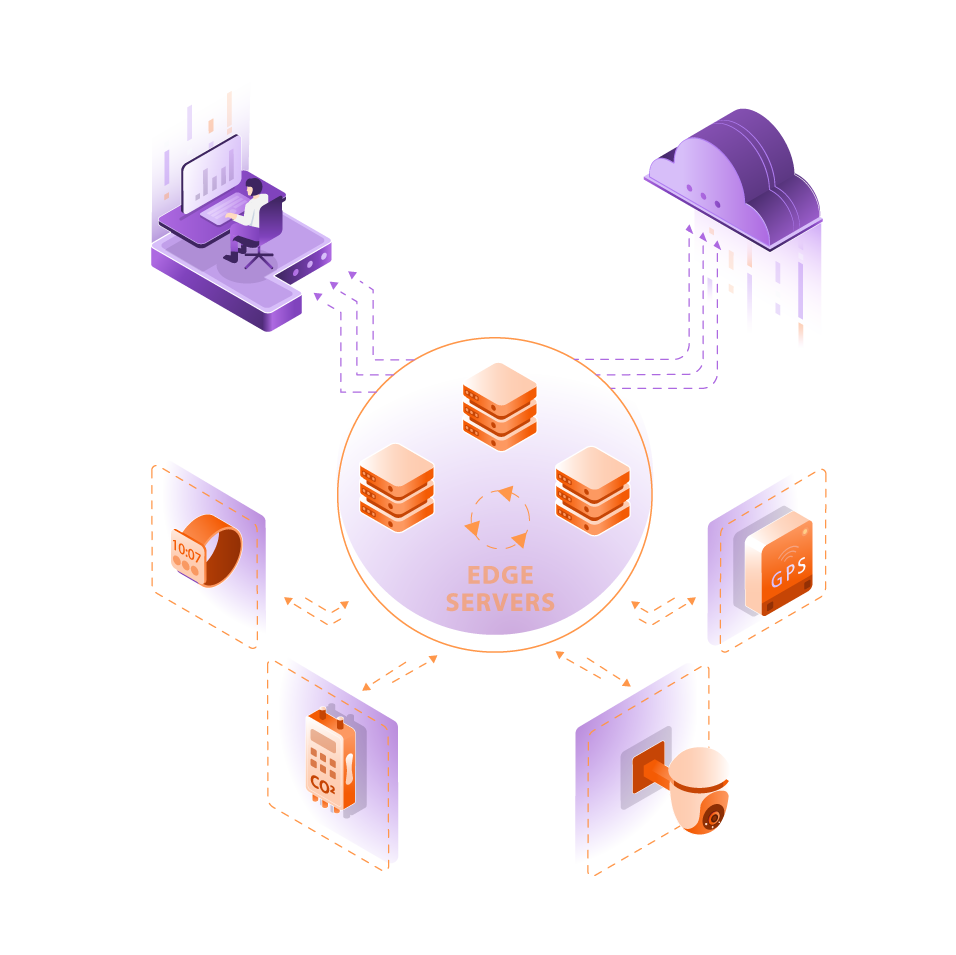
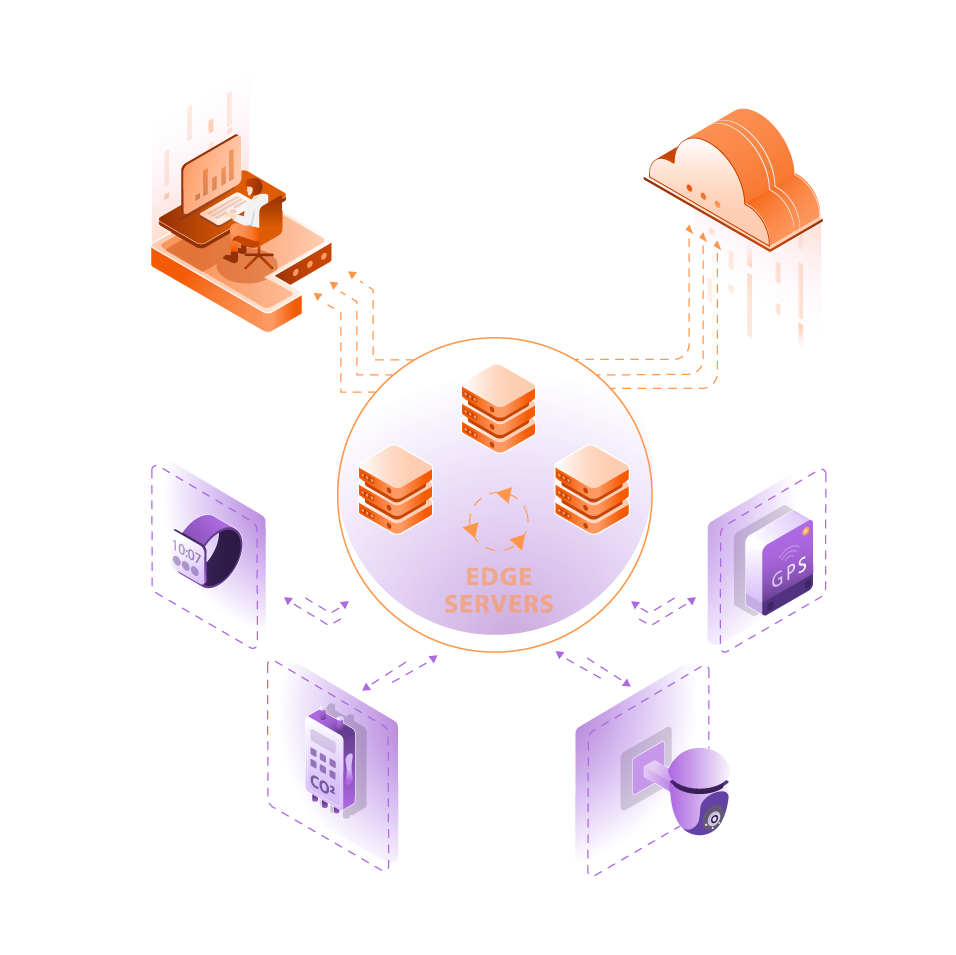
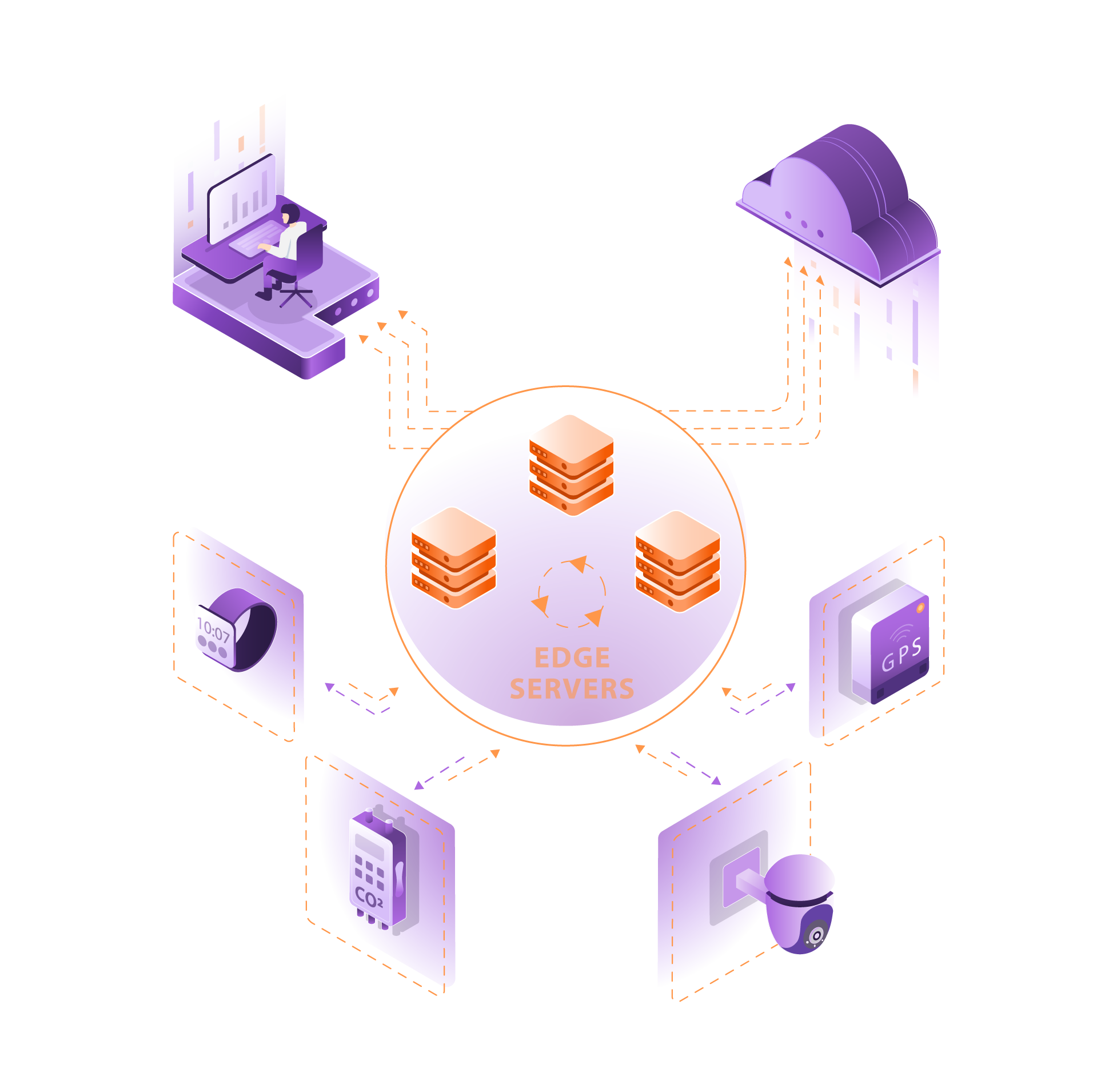
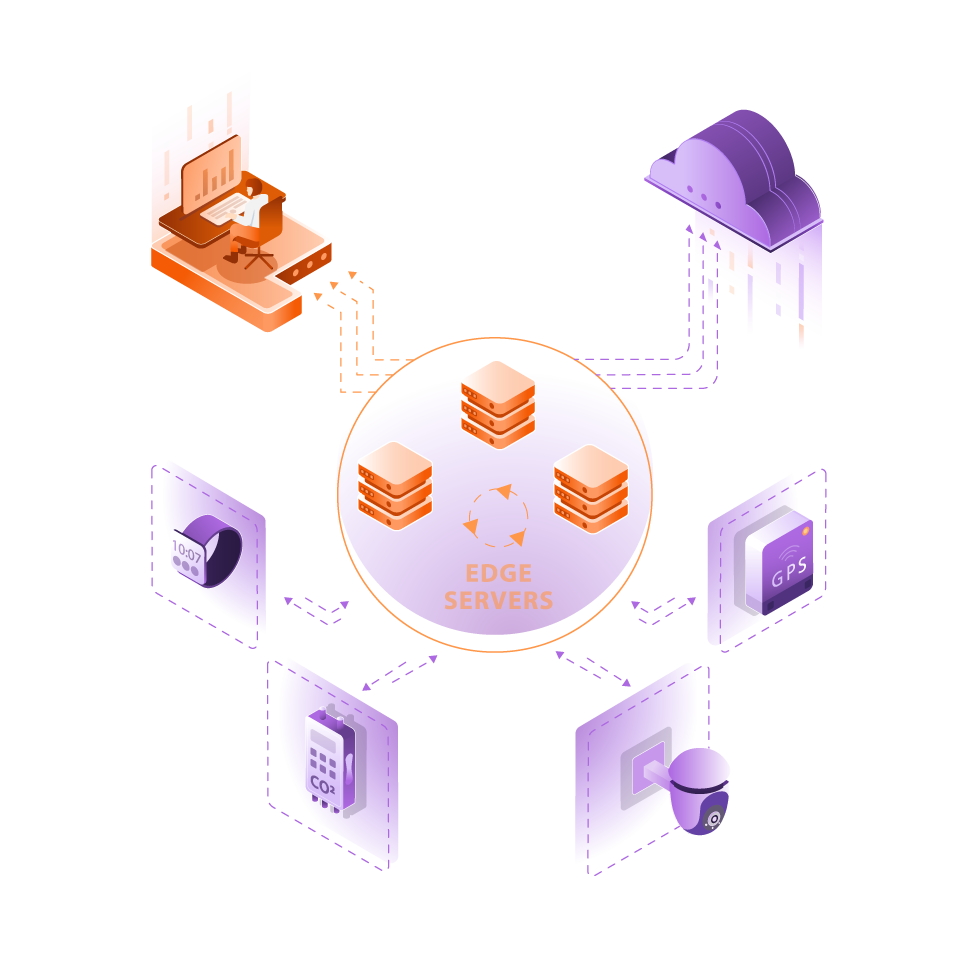
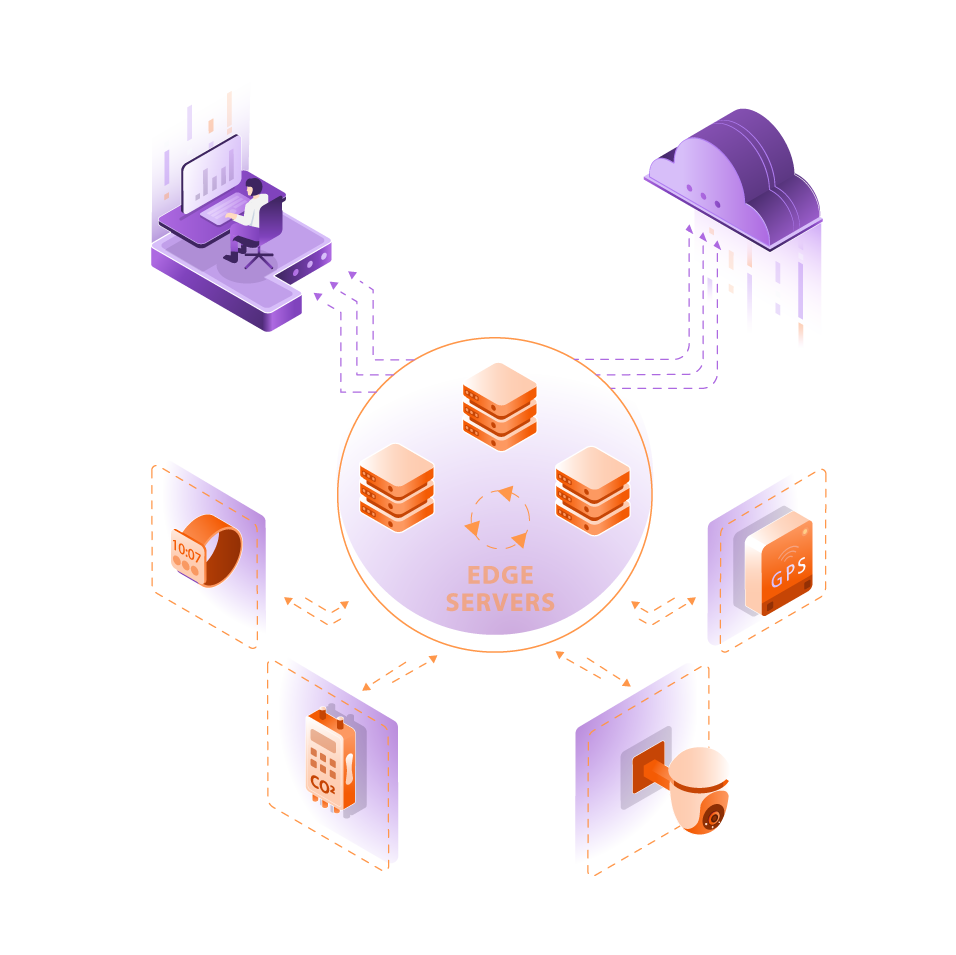
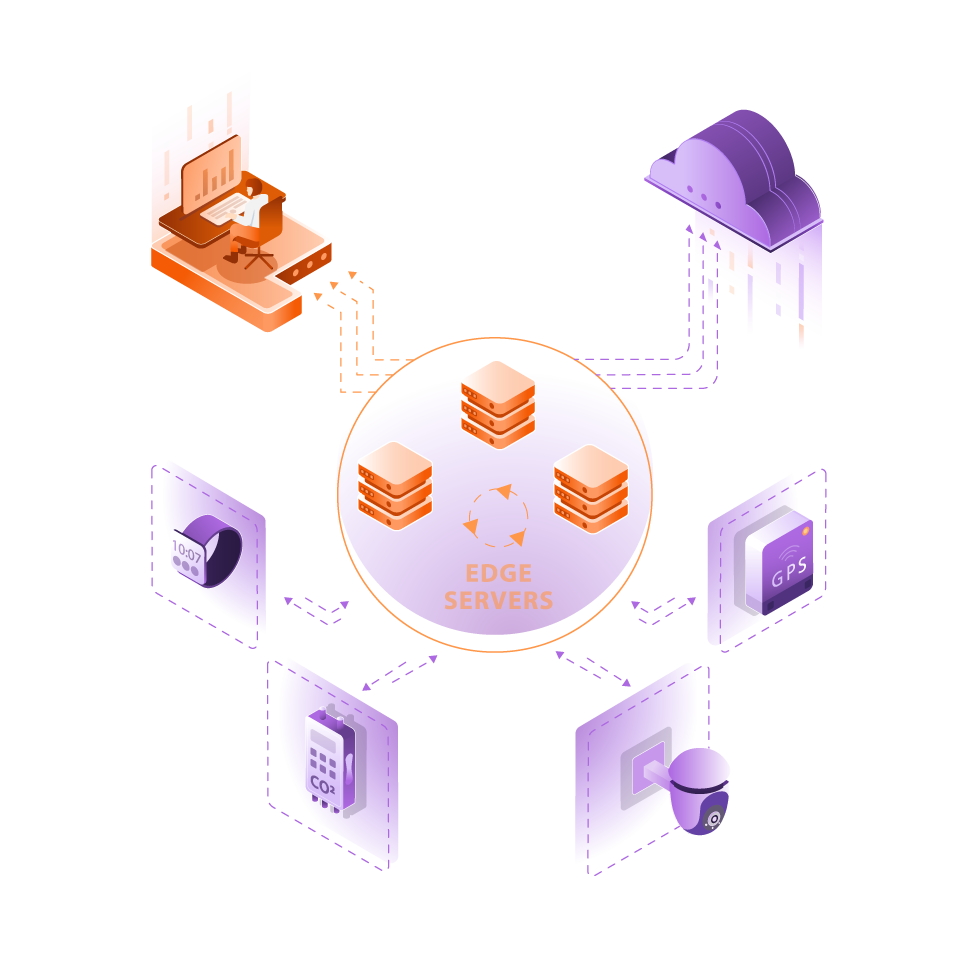
Edge Computing empowers these operations by bringing processing power and intelligence directly to the front line. Data from sensors, cameras, and autonomous systems is analyzed locally, enabling instant decision-making, rapid threat detection, and reliable communication without dependence on external networks.
At Edge Solutions Lab (ESL), we develop edge architectures for defense-grade systems, ensuring secure data handling, continuous operation, and adaptive AI capabilities in mission-critical conditions. Our solutions support real-time analytics, remote orchestration, and continuous software updates for drones — even during flight — maintaining peak performance and system integrity in dynamic field scenarios.
Secure Offline Software Deployment for Military Drones
Challenge:
Modern defense and security operations rely on fleets of autonomous aerial systems — drones equipped with advanced computing for navigation, targeting, and intelligence gathering. Yet these systems face a critical challenge in software lifecycle management: secure, consistent updates in air-gapped or connectivity-restricted environments. In most military contexts, devices cannot remain permanently connected to the internet due to security and operational risks. As a result, software updates are often done manually — retrieving each drone, connecting it via cable, and deploying updates from a laptop. This approach is slow, error-prone, and non-scalable, especially when managing hundreds of deployed drones.
Approach:
Edge Solutions Lab (ESL), in collaboration with Defense Partner Company, set out to demonstrate a secure, air-gapped software delivery workflow for UAVs operating without internet connectivity. The solution integrated Partner open-source tools — Zarf and Kubernetes distribution onto the drone with autonomous capabilities. The goal: enable software and firmware deployment directly to drones in the field, without cables, cloud connections, or manual handling.
Solution & Results:
The integrated system was deployed on active UAVs equipped with onboard edge compute modules (for AI-assisted flight, mapping, and target recognition). Key capabilities included:
- Offline software deployment to drones via local wireless link (Wi-Fi or Bluetooth)
- AirGap-compatible Zarf/UDS integration for verified package delivery and signing
- Real-time update process while drones remain active or airborne
- Tablet-based control interface for operators to push updates within seconds
In live demonstrations, updates were successfully delivered from a nearby tablet to a flying drone over Wi-Fi at distances up to 30 meters, without interrupting the flight. An update package was installed within seconds, validating the feasibility of hands-free, secure field updates for disconnected aerial systems.
Impact:
The collaboration proved that air-gapped software management can extend beyond static infrastructure to mobile robotic systems. The approach eliminates the need to recall drones for manual maintenance, enabling secure, scalable update delivery across distributed fleets. This architecture lays the foundation for future “drone-to-drone” or “operator-to-device” update swarms, where autonomous units propagate verified updates to others in the field — a breakthrough concept for defense, public safety, and industrial robotics.

Why now?
Cloud-to-Edge Convergence Is Becoming Mission-Critical!
Modern defense and public safety operations are increasingly data-driven, autonomous, and distributed across contested or connectivity-restricted environments. Traditional cloud reliance is no longer sufficient for mission tempo, threat response, or operational resilience.
Here’s why leading defense and public safety teams are adopting edge capabilities right now:
5G rollout
5G makes edge technology critical for tactical operations because it links high-speed field connectivity with real-time data processing — enabling bandwidth-heavy missions like autonomous surveillance, mobile command units, and coordinated drone swarms.
Edge-specific compute acceleration
Specialized rugged processors (e.g., TPUs, NPUs, FPGAs) are optimized for tasks such as live video analytics and AI inference on tactical devices, supporting faster situational awareness and local decision-making.
Mature edge platforms
Defense-ready platforms like K3s, AWS Greengrass, Azure IoT Edge, and Google Edge TPU simplify the deployment and management of secure, containerized workloads and AI models across distributed field infrastructure.
Rise of edge-native applications
New mission systems — including tactical traffic control, coordinated UAV fleets, field robotics, and smart emergency response — are being designed from the ground up to operate directly at the edge.
Standardization and interoperability
Standards such as MQTT, OPC UA, and gRPC — along with open, interoperable hardware/software — streamline secure integration across tactical fleets and ensure future-proof multi-vendor deployments.
On-device AI inference
Advances in model compression (e.g., quantization, pruning) enable AI to run directly on drones, rugged sensors, and mobile units, ensuring intelligence remains available even in disconnected or contested environments.
Ready to explore how to bring secure, cloud-grade capabilities to the tactical edge?
The Advantages of Cloud-to-Edge Convergence with ESL
Technical Advantages
Reduced Bandwidth Usage & Tactical Network Efficiency.
Ultra-Low Latency for Mission-Critical Decisions.
Operation Without Reliable Connectivity (Air-Gapped, Denied, or Disrupted Environments).
Energy Efficiency in Field-Deployed Systems.
Freedom from Cloud Vendor Lock-In, Supporting Defense Procurement Needs.
Security Advantages
Data Sovereignty & Local Control.
Reduced Attack Surface.
Tamper-Proof Updates & Packages.
Operational Security in Disconnected Mode.
Compliance With Defense Standards.
Operational Advantages
Real-Time Situational Awareness.
Autonomous Mission Execution.
Resilience in Contested Environments.
Reduced Operator Workload.
Scalable Field Deployment.
Ready to explore how to bring the Cloud Experience to the Edge in your project?
How it’s made?
Mission Platform Feasibility Study at ESL
Our Mission Platform Feasibility Study is the foundation of any successful defense or public-safety edge initiative. At this stage, we evaluate your operational use case, mission constraints, and long-term capability goals to validate whether an edge architecture is the right fit.
We run a structured assessment of existing systems, deployment constraints, interoperability, and potential technical risks that could compromise mission readiness. Based on these findings, we determine whether a Discovery Phase is needed — a deeper exploration that defines mission architecture, technology stack, and an implementation roadmap aligned with operational doctrine.
The result is a data-driven plan balancing mission requirements, security, performance, and lifecycle cost — giving you confidence that each next step leads to a resilient, future-proof capability.
This phase ensures the solution aligns with your mission goals, technical requirements, and budget — while minimizing risk and maximizing operational impact.
Rugged Hardware Design & Development
From initial mission concepts to full-scale production, ESL delivers complete hardware development for defense-grade and public-safety edge systems. We design boards, modules, and rugged devices optimized for extreme conditions — where reliability, survivability, and efficiency are critical.
Our expertise includes electronics and mechanical engineering, covering rugged enclosures, thermal management, shock/vibration protection, and form-factor optimization for UAVs, vehicles, and field equipment. We support rapid prototyping, mechanical models, production tooling, and full system integration.
We work with trusted manufacturing partners in the USA, Germany, and Ukraine, supporting pilot runs through large-scale production while maintaining strict quality, traceability, and compliance standards.
With our end-to-end approach — schematics, PCB layout, prototyping, environmental testing, certification, and mechanical integration — you get mission-ready hardware built for today’s and tomorrow’s environments.
Embedded & Mission Firmware Development
Firmware is the operational backbone of every embedded and tactical system. At ESL, we build secure, optimized firmware for UAVs, autonomous platforms, field sensors, industrial safety systems, and rugged edge devices.
We deliver high-performance, stable, and secure firmware tailored to your hardware architecture and mission profile.
From low-level drivers, communication stacks, and update mechanisms to OTA and air-gapped workflows, we ensure your systems operate reliably under field conditions while maintaining efficiency and security.
Mission Software Design & Development
Mission-critical edge systems require software that is efficient, robust, and secure. We combine rigorous architecture with iterative development to deliver applications that meet the demands of defense, aerospace, and public-safety operations.
Our process includes requirements analysis, modular architecture design, iterative implementation, and maintainability planning.
Whether you need cloud-integrated mission software, hybrid control systems, embedded logic, or AI-driven capabilities, we ensure tight hardware-software integration and dependable edge performance.
Hardware–Software Integration
Operational performance depends on seamless full-stack integration. ESL specializes in deep hardware–software integration — covering firmware, BIOS, OS, middleware, and mission applications.
Through full-stack validation, performance optimization, and stress testing, we reduce latency, minimize power draw, and ensure stable mission performance.
This holistic approach guarantees predictable, reliable operation in real-world and mission-critical environments.
DevSecOps at Edge Solutions Lab
Deployment is not just launching code — it is creating a secure, automated, and repeatable deployment environment for mission systems.
Our team uses Infrastructure as Code (IaC) with tools like Ansible, ensuring standardized, auditable, and scalable automation from cloud to disconnected edge nodes.
We automate deployment, configuration, and scaling of edge platforms using DevSecOps practices tailored to classified, air-gapped, and resilient field environments.
AI & LLM Deployment at the Tactical Edge
Deploying AI at the edge requires solving challenges in bandwidth, compute limits, security restrictions, and hardware diversity. This requires a tight collaboration between ML engineers, DevOps, and mission developers.
We build automated pipelines for distributing, updating, and monitoring edge AI applications, even in remote, contested, or low-bandwidth environments.
For AI models, we handle optimization, quantization, validation, and continuous improvement, ensuring mission-relevant accuracy and performance. Your AI runs close to the data, where mission value is highest.
Hardware & Software Mission Validation
Validation is about trust — trust that your system performs exactly as intended in mission conditions. We design multi-layer validation frameworks spanning component testing, performance checks, environmental stress tests, and security compliance.
Our validation pipelines ensure functionality, resilience, fault tolerance, and operational readiness, enabling systems to withstand harsh environments. Continuous validation accelerates certification and reduces mission risk.
Testing is not a final step — it is an integral part of the entire lifecycle. Every component is verified, tracked, and proven.
Seamless Tactical Edge Scaling
Scaling edge deployments in defense or public safety is complex — ESL makes it predictable. We design platforms that allow entire edge environments to be replicated as templates and deployed across fleets, bases, or distributed units.
Our solutions deliver consistent configuration, centralized orchestration, and mission-aligned scaling across hundreds or thousands of nodes.
Instead of redesigning deployments site by site, you gain a repeatable path from pilot to full-scale rollout. ESL transforms your solution into a scalable mission platform — deploy once, scale anywhere.
Smart, Automated Maintenance
Maintenance for mission systems must be proactive, secure, and automated. Our approach integrates monitoring, updates, and remediation into CI/CD workflows, enabling large-scale systems to be maintained with minimal human effort.
We support remote diagnostics, automated firmware/software updates, and zero-downtime patching across distributed or contested environments.
With ESL, maintenance becomes a strategic advantage — keeping your infrastructure healthy, secure, and mission-ready around the clock.
Ready to explore how to bring the Cloud Experience to the Edge in your project?
Is Cloud-to-Edge Convergence Right for You?
Identify Your Use Case & Constraints
Start by defining the operational scenarios where real-time processing, reduced latency, offline functionality, or data privacy are critical.
Common examples include remote monitoring, AI inference in the field, industrial control systems, or secure data handling at the Edge.
Assess Existing Infrastructure
Evaluate your current hardware, connectivity, software architecture, and data flow.
Are your systems centralized and cloud-dependent? Do you face issues with latency, bandwidth costs, or downtime? This helps highlight where Edge Computing could create immediate value.
Evaluate Scalability & Future Growth
Ask yourself: Will your operations scale across locations, devices, or regions?
Edge architecture allows you to “deploy once, replicate everywhere” — which is ideal for multi-site businesses or distributed assets.
Consider Compliance, Security & Control Need
If you operate in a regulated industry (e.g., healthcare, defense, telecom), Edge Computing helps keep sensitive data local, meet residency laws, and reduce attack surfaces — making it a strategic advantage.
Talk to an Expert
Finally, consult with the Edge Solutions Lab team. We’ll help you assess feasibility, estimate ROI, and determine the most effective way to design and deploy an Edge-native architecture tailored to your needs.
Let’s find out if Edge is the right fit — and what it could mean for your future
The sooner you evaluate your Edge readiness, the faster you can unlock faster response times, smarter automation, and scalable digital operations.
Frequently Asked Questions
What is tactical edge computing, and how does it relate to military operations?
Tactical edge computing refers to the deployment of computing resources closer to the location where data is generated, such as on the battlefield or at forward operating bases. This approach enhances military operations by enabling real-time data processing and decision-making, which is crucial for warfighters in dynamic and often hostile environments.
How do edge computing technologies benefit warfighters?
Edge computing technologies benefit warfighters by providing them with real-time access to critical data, allowing for informed decisions during tactical engagements. This technology reduces latency, enhances network connectivity, and ensures that sensitive information is processed quickly and efficiently even in low-bandwidth environments.
What are use cases of military edge computing?
Common use cases of military edge computing include data fusion from various sensors and IoT devices, command and control systems, and autonomous vehicles. These applications enable improved situational awareness, enhanced automation, and better resource management in military operations.
How does artificial intelligence enhance tactical edge computing?
Artificial intelligence enhances tactical edge computing by enabling advanced data analysis and predictive modeling. AI algorithms can process data at the edge, allowing for faster decision-making and more efficient resource allocation, which is essential for successful military missions.
What challenges are associated with deploying edge computing in military environments?
Deploying edge computing in military environments poses challenges such as ensuring network connectivity in remote or hostile areas, managing limited processing power on edge devices, and maintaining data security. Addressing these challenges is crucial for effective military use of edge computing solutions.
What role do sensors play in military edge computing?
Sensors play a vital role in military edge computing by collecting real-time data that is essential for situational awareness and operational effectiveness. The data from these sensors is processed at the edge, allowing for immediate insights and actions by military units on the front lines.
How does the rise of tactical edge computing impact military strategy?
The rise of tactical edge computing impacts military strategy by enabling more agile and responsive operations. By decentralizing computing resources, military units can deploy computing capabilities closer to the action, improving their ability to react to adversaries swiftly and efficiently.
What is the future of military edge computing?
The future of military edge computing looks promising, with advancements in computing technologies, AI, and automation. As the Department of Defense continues to invest in edge computing solutions, we can expect enhanced capabilities for first responders and warfighters, leading to more effective military operations.